MFA (Multi-factor authentication) has become a required security measure with regards to work and personal accounts. In this quick article, I talk about “Security Defaults” which give you the option to enable MFA on Azure but with quite a few limitations.
There is a misconception that within Azure, You need to purchase an Azure AD Premium 1 license to be able to assign MFA to users logging into Azure. Although Azure AD Premium (https://azure.microsoft.com/en-us/pricing/details/active-directory/) is the recommended approach to enable MFA within Azure, thanks to “Conditional Access” where you can set the conditions when MFA is enforced and test it out on a set on control users along with lots of other benefits. It is still not free and if you are someone who is still starting their Azure journey, you might not be interested in buying the Premium license. Security Defaults might be the solution for you.
Security Defaults can be enabled by going to your Azure Active Directory – Properties – Manage Security Defaults section.
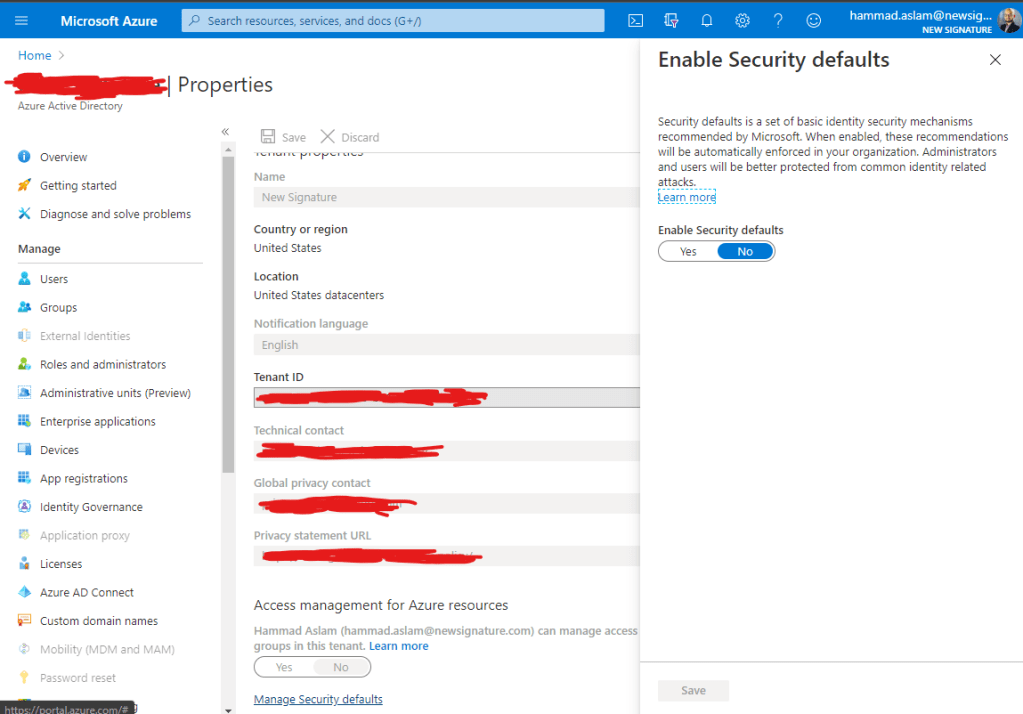
As you can tell from the simplicity of turning the feature on, that it is very limited in terms of its customization. The moment this is turned on, all users will be required to setup their MFA and they can only use the Microsoft Authenticator app. All admins will be required to MFA every time they login but all other users will only be prompted for MFA when required, for example, when logging in from a suspicious IP. The complete details regarding Security defaults can be found here: https://docs.microsoft.com/en-us/azure/active-directory/fundamentals/concept-fundamentals-security-defaults
As shown above, Security Defaults is no way a recommended approach for an Enterprise to set up their MFA solution but for someone just starting within Azure and looking for added security without affecting their wallet, Security defaults does the job.

Leave a comment